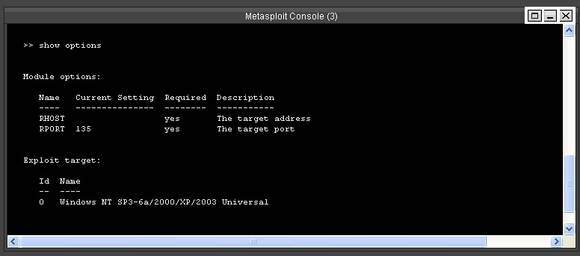
Microsoft Windows Rpc Exploit Metasploit
Windows RPC with Routing and Remote Access enabled in Windows XP and Windows Server 2003 allows an attacker to execute code on a targeted RPC server which has Routing and Remote Access enabled via a specially crafted application, aka 'Windows RPC Remote Code Execution Vulnerability.' Publish Date : 2017-06-15 Last Update Date : 2019-10-02
- CVSS Scores & Vulnerability Types
- Products Affected By CVE-2017-8461
- Number Of Affected Versions By Product
- References For CVE-2017-8461
| |||||||||||||||||||||||||||||||||||||||||||||||||||||
- Metasploit Modules Related To CVE-2017-8461There are not any metasploit modules related to this CVE entry (Please visit www.metasploit.com for more information) |
The Metasploit RPC allows you to display hosts, services and vulnerabilities from the Metasploit database within Serpico. Once setup, you can automatically map vulnerabilities from a workspace into your Serpico report. The hosts and services in the metasploit database can also be used in your report, for exemple as an appendice.
Jan 05, 2008 Hacking Windows XP: MSRPC vulnerabilities. Hacking Windows XP: MSRPC vulnerabilities. How to exploit a Windows 7 PC using Metasploit - Duration: 9:30.
Enable Vulnerability Mapping feature
Log in as an Administrator, Under the 'Maintenance Menu' on the Left hand side of the screen, select 'Modify Configuration'
Check the box labeled 'vulnmap' and click 'save'.
Restart Serpico for changes to apply.
Start Metasploit RPC server
On the system you have Metasploit installed on, issue the following command to start the Metasploit RPC service:
sudo msfrpcd -U msfuser -P msfchangeme --ssl
For additional information or troublshooting, see the following wiki page: https://github.com/rapid7/metasploit-framework/wiki
You must have MSF RPC working before moving on.
Configure Metasploit connector in Serpico
Next access the report for which you want to configure the Metasploit RPC connector for.
Pete's XGL2 Linux PSX GPU. This is the Linux port of the OpenGL2 plugin. It needs a modern card and up-to-date Linux drivers (requires FBOs or pbuffers, ATI's 'render-to-texture' ability is also supported)! Pete's GPU archive (all versions) Pete's MesaGL Linux GPU Version 1.77 (178 KByte TAR.GZ-File) - visual rumble feature (epsxe 1.7.0), special game fix 'fake gpu busy', adjusted fps limit Pete's OpenGL2 PSX GPU Version 2.8 (170 KByte Zip-File) - New stretching modes, ultra high internal Y resolution, OGL2InvSize shader param, framebuffer objects support.
 Description Quote from Pete's page: 'This is an hw/accel psx und ZiNc gpu plugin for modern systems! It doesn't use OpenGL2 (yet), but you will need a good gfx card supporting the latest OpenGL extensions. NVidia/ATI cards with at least 64 MB (ZiNc: 128 MB) vram are recommended!'
Description Quote from Pete's page: 'This is an hw/accel psx und ZiNc gpu plugin for modern systems! It doesn't use OpenGL2 (yet), but you will need a good gfx card supporting the latest OpenGL extensions. NVidia/ATI cards with at least 64 MB (ZiNc: 128 MB) vram are recommended!'On the Left hand side select 'Additional Features'
Under Additional Features select 'Configure a Metasploit RPC Connection'
Configure Metasploit RPC Settings:
To test the Metasploit connection, select 'Hosts' under 'Metasploit Data management' menu on the left (when editing a report). If hosts exist in your workspace, they will be displayed in Serpico. If you get an error, double check that Serpico can communicate with the msfrpcd listener.
Example of hosts information:
Example of vuln information:
Automatically Map Vulnerabilities
Each Serpico finding you want anatomically mapped will have to have a CVE (or other supported ID) assigned to the finding. This is done by editing the finding in the findings database. More information on what IDs are supported can be found by clicking on the 'Add new vuln mapping ID' button:
Once mappings exist, if your Metasploit workspace contains a vulnerability matching the mapping, the finding will be automatically added.
To automatically map findings, edit a report that has a Metasploit connection, then choose 'Additional Features', and select 'Auto Add Vulnerabilities from Metasploit DB':
Troubleshooting
- msfprcd without SSL is NOT supported. You must provide the --ssl switch when starting msfrpcd.
- Do not use 'load msgrpc' within msfconsole, instead launch via the command line tool msfrpcd.
- Use only supported Ruby versions. (currently 2.1.5, other versions have been known to break msf rpc functionality)
- Before submitting an issue, make sure you have verified traffic with tcpdump/wireshark, and confirm your Ruby version.
Reporting on Services from the Metasploit database
In your template you can
Insert services that were discovered during the assessment :
æreport/services/serviceæ ∞host∞ ∞port∞ ∞name∞ ∞info∞Insert hosts that were discovered during the assessment :
æreport/services/serviceæ ∞address∞ ∞os_name∞ ∞info∞Insert number of telnet port found into the template :
πcount(report/services/service/port[text()='23'])πTest if a port was found, and display the test you usually do on this port :
†report/services/service/port[text() = '161']†We found SNMP services, so we did the following test on it ://your test¥
Here's the full data accessible :
¬report/hosts/host¬
created_at
addres
mac
namestate
os_name
os_flavor
os_sp
os_lang
updated_at
purpose
info
∆
¬report/services/service¬
host
created_at
updated_at
port
proto
state
name
info
∆